Clear Sky Science · en
Blockchain-enabled identity management for IoT: a multi-layered defense against adversarial AI
Why protecting connected gadgets now needs new tricks
Homes, hospitals, factories, and cities are filling up with internet-connected gadgets, from smart locks and cameras to medical sensors and power-grid controllers. These devices often run quietly in the background, but if their identities are faked or stolen, criminals—or hostile states—can unlock doors, hijack equipment, or shut down services. This paper explores a new way to protect the “who’s who” of the Internet of Things (IoT) using blockchain and advanced cryptography to stay ahead of increasingly clever artificial intelligence (AI) attacks.

What goes wrong with today’s trust systems
Most connected devices today rely on central authorities, such as certificate servers, to prove who they are. If one of these central hubs is hacked, an attacker can impersonate huge numbers of devices at once. At the same time, AI tools—especially generative models—can forge biometric signals and behavioral patterns that look almost real, fooling face or heartbeat scanners and even imitating how you type or move a mouse. The authors note that more than four out of five IoT systems remain vulnerable to such advanced tricks. They also highlight that many existing blockchain “smart contracts,” the small programs that automate actions on a blockchain, contain hidden bugs that AI-driven attackers could exploit.
Building a shared, tamper-proof phonebook for devices
The proposed system replaces the single, central authority with a shared ledger based on blockchain technology. Each IoT device creates a cryptographic key pair, and only a one-way scrambled version (a hash) of its public key is stored on the chain as its permanent ID. This makes the identity record tamper-resistant and extremely hard to forge. Before a device is accepted, it must pass a liveness test—showing that its biometric signal or other physical signature truly comes from a real, present device rather than from a generative model—and then prove, in a privacy-preserving way, that it holds the matching private key. A committee of independent validators checks this proof and votes on whether to approve the device, so no single party can silently push fake devices into the system.
Adding smart contracts, learning, and behavior into the defense
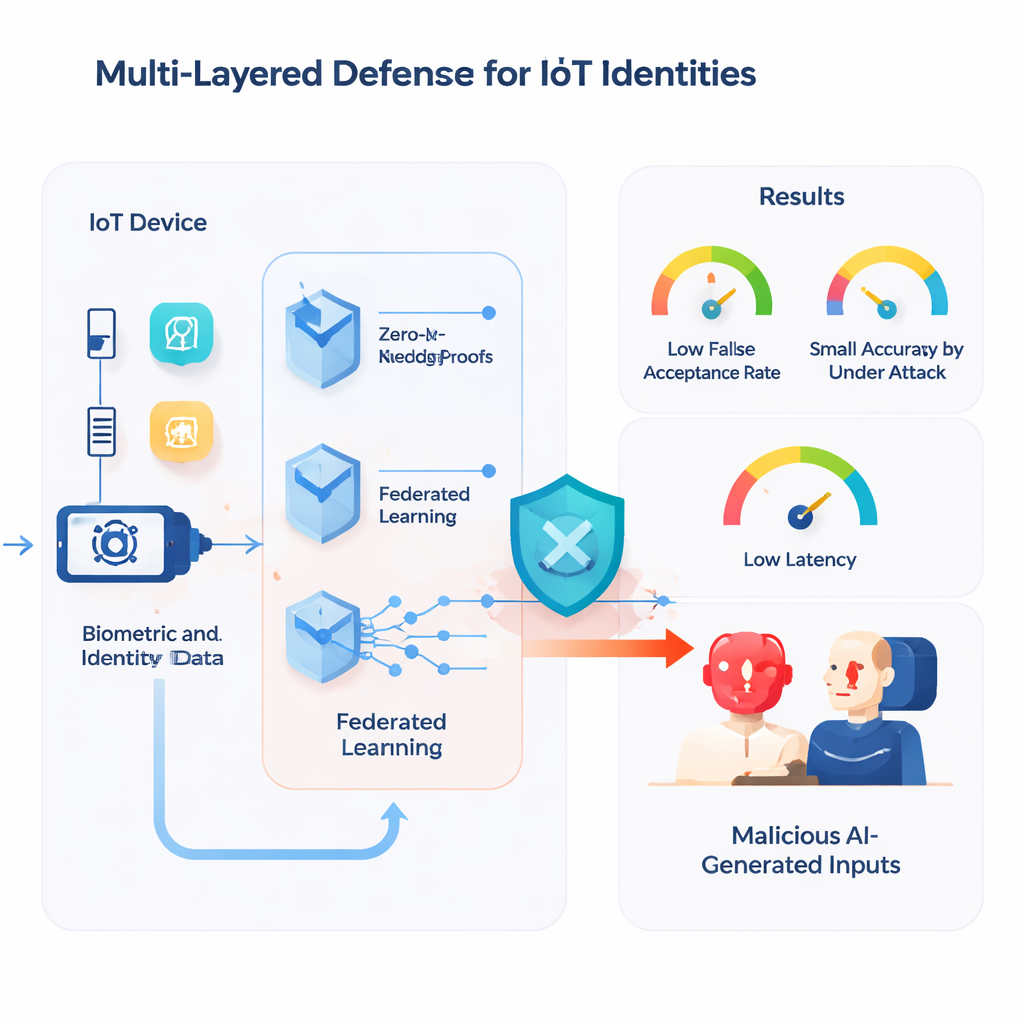
On top of this identity layer sit smart contracts that automatically manage device lifecycles: registration, verification, revocation, and access control. These contracts are written to follow strict, formally checked rules so that, for example, a device cannot be registered twice under different guises. To guard against AI attacks that try to corrupt shared machine-learning models, the system uses a robust form of federated learning: devices train models locally and send only updates, which are then filtered by an algorithm that discards suspicious contributions. The authors also fold in behavioral biometrics at the user interface level, learning a person’s typical typing and mouse patterns. If live behavior deviates too far from the learned profile, the system can demand extra authentication or block access, helping to thwart deepfake-based phishing screens.
Keeping wallets and software honest under pressure
Because users interact with the system through digital wallets and web interfaces, those components are also given extra protection. Sensitive actions, such as revoking a critical device or changing credentials, require threshold signatures—multiple trusted parties must each add a partial approval before the blockchain will accept the transaction. An embedded AI model watches for unusual patterns in transaction fees or activity bursts that might signal bots or automated fraud. Behind the scenes, the authors test their smart contracts in a simulated blockchain environment that mimics real-world conditions, then bombard them with automatically generated “weird” inputs designed to expose rare bugs or vulnerabilities before deployment.
How well the layered shield stands up to AI attackers
The team built a working prototype using Ethereum tools, a React-based front end, and popular wallets such as MetaMask. They then staged a series of adversarial tests. AI-generated biometric spoofs were used to try to sneak fake devices through registration, machine-learning models were intentionally poisoned, and crafted transactions attempted to bypass wallet protections. In these experiments, the system kept the false acceptance rate for spoofed biometrics to just 0.07%, limited model accuracy loss under poisoning to about 1.5%, and verified privacy-preserving proofs in roughly 142 milliseconds on modest edge hardware—fast enough for many real-time IoT uses. No fraudulent transactions were accepted in their test scenarios, and formal tools confirmed that key contract rules, like preventing duplicate registrations, held across all explored cases.
What this means for everyday connected life
Put simply, the study shows that it is possible to give billions of low-cost devices a more reliable “passport” that is hard for AI-powered impostors to fake, without slowing the system to a crawl. By combining blockchain’s shared record-keeping, mathematical proof techniques that hide secrets, careful vetting of automated code, and smarter handling of behavior and learning, the authors outline a practical blueprint for making IoT ecosystems both safer and more resilient. As attackers lean more on AI, defenses like this multi-layered identity framework may become a cornerstone for securing everything from home gadgets to hospital equipment and national infrastructure.
Citation: Usama, M., Aziz, A., Alasbali, N. et al. Blockchain-enabled identity management for IoT: a multi-layered defense against adversarial AI. Sci Rep 16, 4371 (2026). https://doi.org/10.1038/s41598-026-35208-y
Keywords: Internet of Things security, blockchain identity, adversarial AI, zero-knowledge proofs, federated learning