Clear Sky Science · en
Digital watermarking for virtual physically unclonable function data concealment and authentication
Why hidden marks on data matter
Every day, billions of small devices—smart meters, sensors, cameras, and wearables—quietly send data over the air. If an attacker can listen in or replay what they hear, they may be able to pretend to be your device and slip into the network. This paper explores a new way to protect such tiny devices by hiding an invisible “mark” inside the data they send for identity checks, adding an extra lock on the door without adding bulky hardware or heavy computation.
A digital fingerprint for each tiny device
Many secure systems already rely on a kind of digital fingerprint called a Physically Unclonable Function, or PUF. A PUF uses tiny, uncontrollable variations in a device’s electronics to produce responses that are extremely hard to copy. When a server sends a challenge—a kind of question—the device answers with a response shaped by its unique circuitry. Matching challenge–response pairs let the server tell genuine devices from impostors. But classic PUFs need special hardware, age over time, and can still be studied and imitated by clever attackers. To get around these limitations, the authors previously built a “virtual PUF” (VPUF) using a neural network: software that learns to mimic the unpredictable behavior of a real PUF while running on ordinary, low‑cost hardware.
Threats in the air between device and server
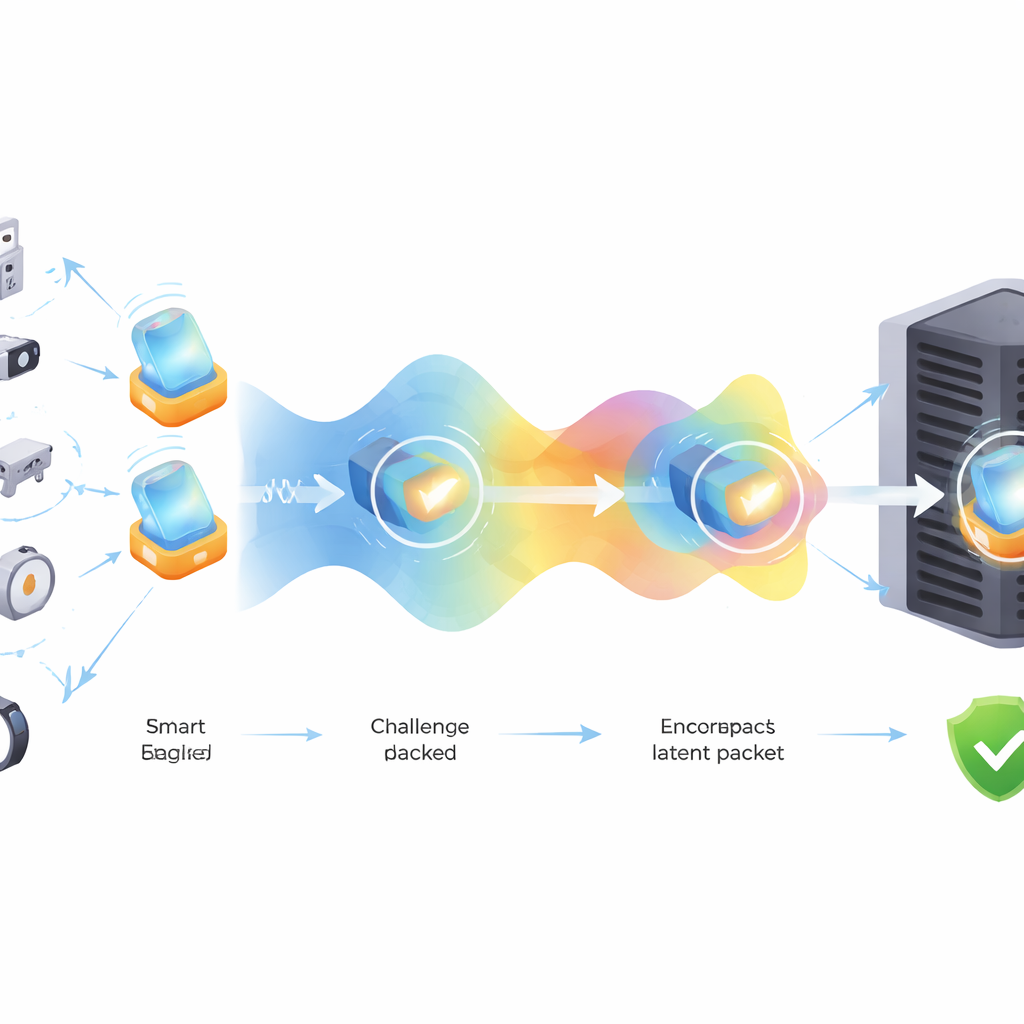
Even with a VPUF, one weak point remains: the messages flying through the wireless channel. In the split‑learning design used here, an encoder on the device transforms each challenge into a compact internal code, called a latent representation, and sends only this code to a decoder on the server. That already hides raw data, but if an eavesdropper records enough of these codes, they might still reverse‑engineer the system, or simply replay old codes to fool the server. The problem is to protect these in‑between codes so that intercepted signals are useless to outsiders, yet still allow the server to authenticate the device quickly and accurately.
Hiding a moving secret inside the signal
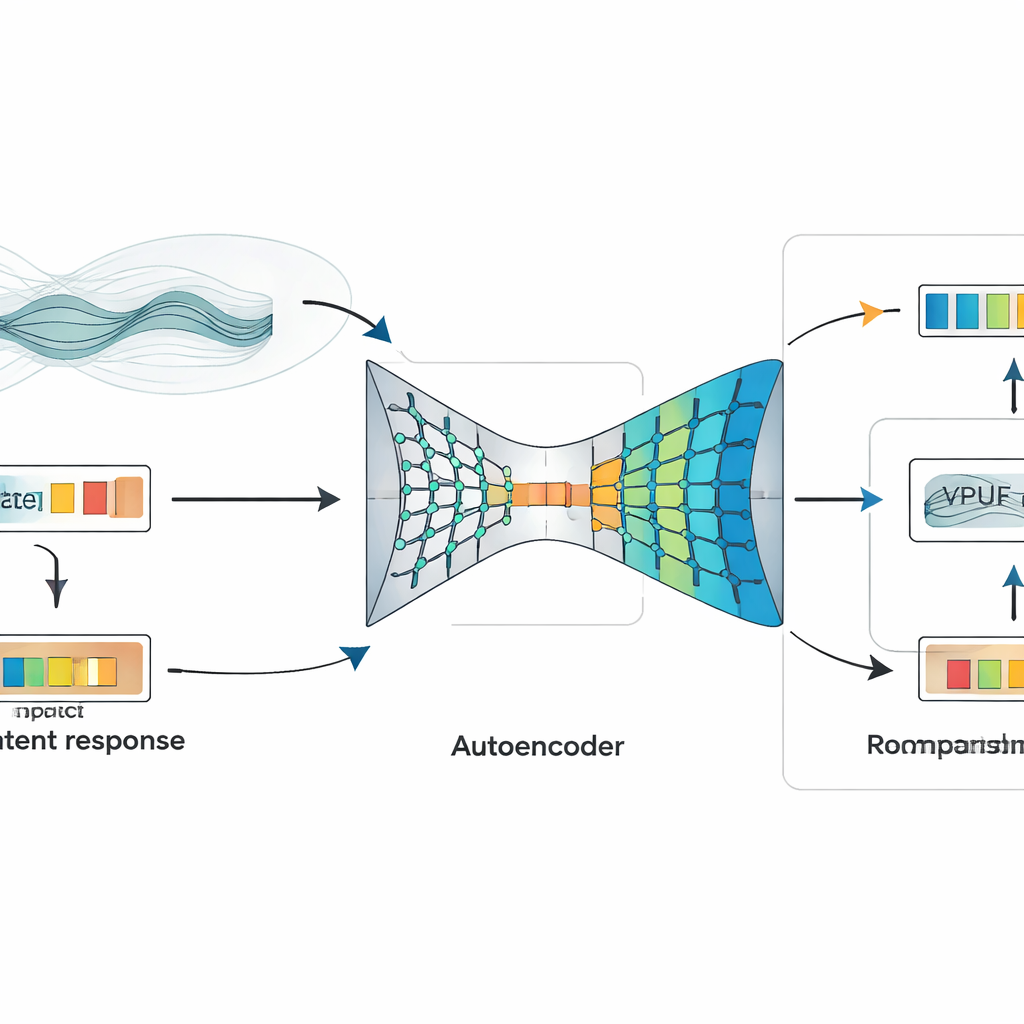
The core idea of the paper is to hide an extra, meaningful mark—a digital watermark—inside the VPUF’s latent code before it leaves the device. Instead of using a fixed, meaningless pattern, the watermark is built from the quirks of the radio channel itself. Wireless signals bounce, scatter, and fade as they travel; engineers describe this with models of “Rayleigh fading.” The authors simulate this fading with a standard model and feed the resulting signal variations into an autoencoder, a neural network that learns to compress data into a tight internal code. This compressed code becomes the watermark. The device then fuses this watermark with the VPUF’s latent response using another lightweight autoencoder, producing a single watermarked code that is sent over the air.
Two locks, one lightweight design
On the server side, a matching network unwinds the watermarked code, separating it back into a predicted VPUF latent response and an estimated watermark. The predicted response goes through the VPUF decoder to give the expected answer for the original challenge. In parallel, the extracted watermark is compared to what the server expects from its own view of the channel conditions. Only if both pieces—the VPUF response and the watermark—check out does the system accept the device. In tests, this extra processing kept the authentication accuracy at about 99 percent, showed near‑perfect recovery of the watermark under normal conditions, and resisted random attempts to forge a valid watermark even after ten thousand tries.
Balancing strength, stealth, and cost
The authors also probe how the scheme behaves under noise, mimicking attackers who try to disturb transmissions to erase or scramble the watermark. The system remains reliable up to moderate noise levels, after which watermark recovery drops while overall authentication accuracy stays high. This reflects a deliberate choice: the method is tuned for low computing cost and strong identity checks rather than maximum toughness against extreme interference. Because everything happens inside compact neural networks working on small codes, the approach fits the tight memory and power budgets of many Internet‑of‑Things devices.
What this means for safer connected devices
In plain terms, the paper shows that it is possible to tuck a moving, environment‑dependent secret inside the already‑compressed identity data that tiny devices send for authentication. That hidden mark both scrambles the signal for prying eyes and gives the server a second, independent way to check who is talking. The result is a flexible, software‑based security layer that can run on modest hardware yet makes eavesdropping, replay, and copy‑cat attacks much harder. While further real‑world testing is needed, especially under more powerful attacks, this latent‑space watermarking strategy points toward more trustworthy networks of small, inexpensive devices.
Citation: Khan, R., Saleh, H., Mefgouda, B. et al. Digital watermarking for virtual physically unclonable function data concealment and authentication. Sci Rep 16, 10472 (2026). https://doi.org/10.1038/s41598-026-35159-4
Keywords: IoT security, digital watermarking, device authentication, neural networks, wireless channels