Clear Sky Science · en
Post-quantum cryptographic authentication protocol for industrial IoT using lattice-based cryptography
Why Future-Proofing Factory Devices Matters
Factories, power plants, and smart cities increasingly rely on small networked gadgets—sensors, controllers, and gateways—that quietly keep machines running and data flowing. The encryption that protects these industrial gadgets today was designed for ordinary computers. As powerful quantum computers emerge, that protection could eventually crack. This paper asks a practical question: can we upgrade the security of industrial Internet of Things (IIoT) devices now, using new “post‑quantum” tools, without slowing them down or overloading their limited hardware?

A New Kind of Lock for a New Kind of Computer
The authors start by explaining why today’s digital locks are at risk. Common methods such as RSA and elliptic‑curve cryptography are built on math problems that quantum algorithms can solve dramatically faster than classical machines. To prepare, standards bodies like NIST have been running a multi‑year process to select new cryptographic tools that should withstand quantum attacks. Among the front‑runners are lattice‑based techniques, which rely on navigating high‑dimensional grids that are believed to be hard for both classical and quantum computers to untangle. Two such tools—Kyber for exchanging keys and Dilithium for digital signatures—have now been standardized and are strong candidates to protect long‑lived industrial systems.
Bringing Post‑Quantum Security into Real Industrial Networks
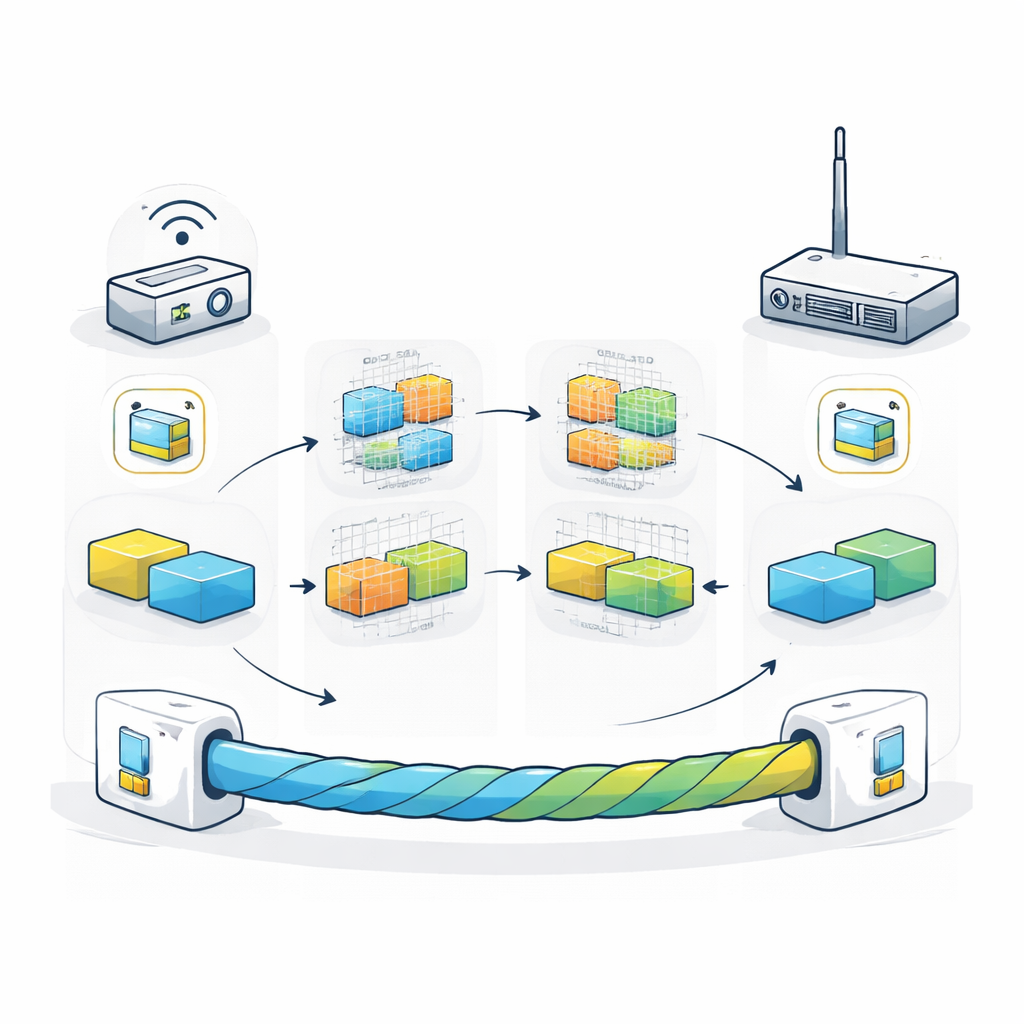
Industrial networks are not like office laptops on a fast corporate Wi‑Fi. They combine tiny battery‑powered sensors, modest gateway boxes, and powerful backend servers, all expected to run for years, sometimes decades. The team focuses on this three‑tier model and weaves Kyber and Dilithium into the familiar TLS 1.3 protocol that already secures web traffic worldwide. They redesign digital certificates, which prove device identity, so that they carry Dilithium public keys and signatures instead of RSA or elliptic‑curve ones. At the same time, they replace the usual key‑exchange step in the TLS handshake with Kyber’s key‑encapsulation mechanism, which creates a shared secret between two devices in a way that is intended to resist future quantum decryption.
Fitting Stronger Security onto Small Devices
A major concern is whether these new tools are too heavy for constrained hardware. To explore this, the authors implement their scheme on a Raspberry Pi 4, a popular, low‑cost single‑board computer often used as an IIoT gateway. Using an open‑source “post‑quantum‑ready” version of the TLS stack and certificate tools, they measure how long key generation, key exchange, and signing operations take, how much memory they consume, and how large the resulting certificates and handshake messages become. They test several strength levels of Kyber and Dilithium and compare them against traditional methods like elliptic‑curve Diffie–Hellman.
What the Experiments Reveal
The results are encouraging. On the Raspberry Pi 4, complete post‑quantum TLS 1.3 handshakes reliably finish in under about 15 milliseconds, which is comparable to or even better than some classical setups in their tests. The extra computational work of Kyber and Dilithium themselves is not the main slowdown; instead, the dominant overhead comes from the size of the new certificates, which can be several times larger than older ones. Even so, memory use stays under roughly 100 kilobytes of heap on the gateway platform—well within what such devices can typically spare. The authors show how different “profiles” of algorithm strength can be matched to each tier: lighter settings for tiny sensors, moderate ones for edge gateways, and the strongest options for central servers and critical infrastructure.
Limits Today and Paths for Tomorrow
The study also outlines what it does not yet cover. All tests run on a single type of hardware over a local loopback connection, so they do not include real‑world network delays, wireless interference, or extremely small microcontrollers with only kilobytes of memory. Energy consumption is not measured, which will matter for battery‑powered gateways. Nonetheless, the work aligns with current government and industry roadmaps that urge migration to post‑quantum methods, and it offers concrete, reproducible numbers that equipment makers and operators can use when planning upgrades.
What This Means for Everyday Industrial Security
In plain terms, the paper shows that it is already practical to shield industrial networks against future quantum decryption—at least at the gateway and server level—without sacrificing responsiveness. By plugging Kyber and Dilithium into standard TLS 1.3 and certificate formats, and by carefully choosing parameters for different device classes, the authors demonstrate a clear migration path: stronger, quantum‑resistant locks that can be rolled out using familiar protocols and affordable hardware. For operators of factories, utilities, and other critical systems, this means they can start future‑proofing their communications today, rather than waiting for quantum computers—and attackers—to catch up.
Citation: Shahid, A.B., Mansoor, K., Bangash, Y.A. et al. Post-quantum cryptographic authentication protocol for industrial IoT using lattice-based cryptography. Sci Rep 16, 9582 (2026). https://doi.org/10.1038/s41598-025-28413-8
Keywords: post-quantum cryptography, industrial IoT security, lattice-based encryption, TLS 1.3, quantum-safe authentication